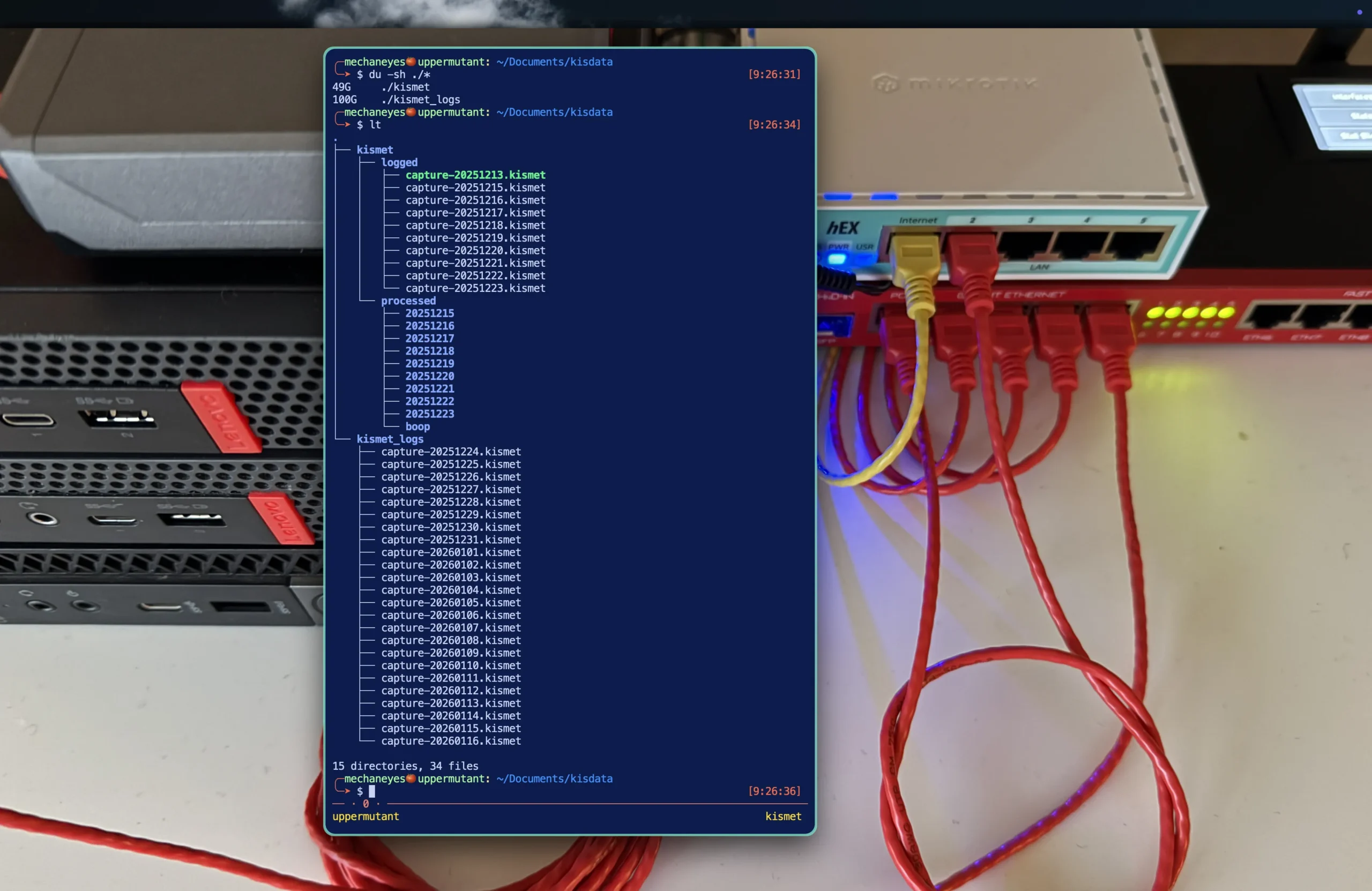
I’ve just closed out the Kismet process I had running around the clock for just over a month.
In that month the database files, which I had rotating daily were typically growing to 5GB before flipping. The total data collected is roughly 150GB.
$ du -sh ./*
49G ./kismet
100G ./kismet_logs
# And the log files themselves
┌── kismet
│ ├── logged
│ │ ├── capture-20251213.kismet
│ │ ├── capture-20251215.kismet
│ │ ├── capture-20251216.kismet
│ │ ├── capture-20251217.kismet
│ │ ├── capture-20251218.kismet
│ │ ├── capture-20251219.kismet
│ │ ├── capture-20251220.kismet
│ │ ├── capture-20251221.kismet
│ │ ├── capture-20251222.kismet
│ │ └── capture-20251223.kismet
│ └── processed
│ ├── 20251215
│ ├── 20251216
│ ├── 20251217
│ ├── 20251218
│ ├── 20251219
│ ├── 20251220
│ ├── 20251221
│ ├── 20251222
│ ├── 20251223
│ └── boop
└── kismet_logs
├── capture-20251224.kismet
├── capture-20251225.kismet
├── capture-20251226.kismet
├── capture-20251227.kismet
├── capture-20251228.kismet
├── capture-20251229.kismet
├── capture-20251230.kismet
├── capture-20251231.kismet
├── capture-20260101.kismet
├── capture-20260102.kismet
├── capture-20260103.kismet
├── capture-20260104.kismet
├── capture-20260105.kismet
├── capture-20260106.kismet
├── capture-20260107.kismet
├── capture-20260108.kismet
├── capture-20260109.kismet
├── capture-20260110.kismet
├── capture-20260111.kismet
├── capture-20260112.kismet
├── capture-20260113.kismet
├── capture-20260114.kismet
├── capture-20260115.kismet
└── capture-20260116.kismet
In that processed directory is data I experimented with early on. I hadn’t and still haven’t put much time into it, but was mostly curious about how discreet, as in how unique individual devices are. Much of it generally is.
It’s really not about the static devices around me. I’m more focused on the devices passing my apartment window.
Turns out it was trivial to identify an individual device and recognize it every time it passed by. Creepy. Yes. Alarming. Also yes.
We bleed massive amounts of data as we walk down the street. I want to know what that data is, and from that, how that data might be used by others. That data you’re (un)knowingly sharing is being collected on a massive scale, then is turned around and sold to just about anyone who’s interested in paying for it.
The United States has some of the most disgracefully absent privacy laws in the world. Advertisers have found that your data is especially valuable, allowing them to build profiles to better target you with ads. They know an astonishing amount of information about us.
Many say they know more about us than we do ourselves.
I have lots to share about this. In the coming days and weeks, as I dive into and start working with the data, I’ll expand on what that data actually is, how it’s being used and what you might consider in adjusting—or not—your habits with that information in mind.
While transforming this data into information, it will simultaneously be transformed into visual form. Exactly what that will look like I’m unsure of at the moment. I like to see where an idea takes me, and to watch how the process governs the eventual shape it takes.
Maybe this knowledge prompts you to make adjustments. Maybe you’ll become aware of these things and simply move on as, who knows, your unknowingly surrendered data might make the groceries in your cart cheaper than the identical groceries in the cart of the person behind you. However, maybe the algorithm thinks you’re rich. Prepare to pay more for that flight (via Harvard’s Berkman Klein Center for Internet & Society).